
Key Challenges in Managing Sensitive Customer Data Online
Managing sensitive customer data online is a constant balancing act between usability and security. Businesses must protect personal information while…
Security isn’t just a buzzword—it’s a way of life. In this category, I share my knowledge on safeguarding your digital and physical world. You’ll find articles on cyber-threats, password hygiene, encryption, VPNs, and tips to secure your devices. I also cover real-world safety, including home security systems, safe travel practices, and protecting your valuables. My goal is to make security simple, practical, and accessible. Whether you’re a tech enthusiast or a concerned parent, you’ll gain insights into preventing hacks, avoiding scams, and staying one step ahead of attackers. From understanding the latest threats to learning how to spot phishing emails, each post empowers you to take control of your security.

Managing sensitive customer data online is a constant balancing act between usability and security. Businesses must protect personal information while…

Digital marketing runs on data and technology, making it a prime target for cyber threats that many businesses overlook. From…

Safeguarding personal and organizational data has never been more critical. As cyber threats advance, privacy laws worldwide are evolving to…

Password managers are essential for digital security, and LastPass was the go-to choice for years. But security breaches and policy…

Penetration testing is how organizations find vulnerabilities before attackers do. But choosing between manual and automated approaches isn't straightforward. Both…

The exploitation phase is where penetration testing gets real. This is the stage where testers actively attempt to breach systems…
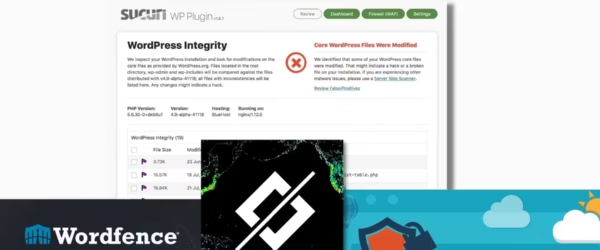
WordPress powers 43% of the web, making it the biggest target for hackers. A security plugin is non-negotiable if you're…

Managing passwords in 2026 without a password manager is a security risk. Reusing passwords, writing them on sticky notes, or…

I've been cleaning up malware-infected Windows machines since 2009. The antivirus landscape has changed dramatically since then. Free options have…

VPNs promise online anonymity, but the reality is more nuanced. I explain what VPNs actually do and don't do for…

VPNs and proxy servers both mask your IP address, but they work very differently and offer different levels of protection.…

Losing your Android phone is stressful, but recovery apps can help you locate, lock, or wipe your device remotely. I've…