5 Best Hardened Base Images for Kubernetes Deployments in 2026
A single bad base image can wreck a cluster before anyone notices. One vulnerable layer, reused across 40 microservices, and suddenly your CVE dashboard lights up like a Christmas tree. Kubernetes didn’t invent that problem. It just multiplied it.
I’ve spent enough time untangling container inheritance to know where most teams lose: not in the application code, but in the foundation they build on. Pick a loose base image and you’ll spend the next quarter chasing Trivy reports instead of shipping. Pick a hardened one and half those tickets never exist. That’s the whole argument. The rest of this piece is which hardened images are actually worth standardizing on in 2026, and which ones fit which kind of team.
What to look for in a hardened base image
Before getting to the shortlist, here’s the checklist I run every image through. Not theory. These are the eight questions that decide whether an image gets near production or gets blocked at the registry.
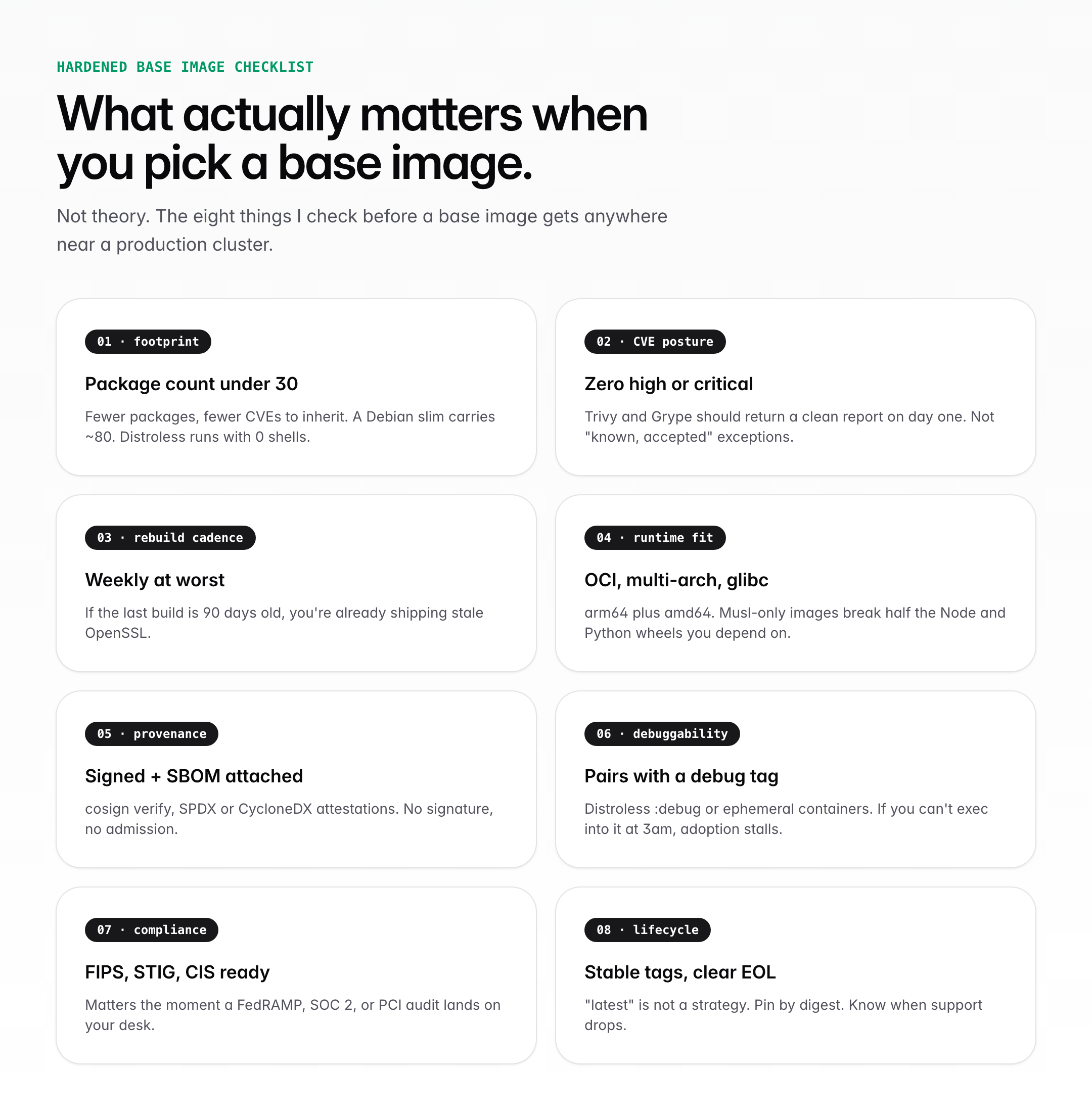
- Package footprint. Under 30 installed packages is the target. A Debian slim image carries around 80. Every package is another CVE waiting to be inherited.
- CVE posture on day one. A clean Trivy or Grype scan, not a spreadsheet of “known, accepted” exceptions. If the baseline isn’t zero high or critical, you’re starting in the red.
- Rebuild cadence. Weekly at worst. If the last build is 90 days old, you’re already shipping stale OpenSSL.
- Runtime fit. OCI compliant, multi-arch (arm64 plus amd64), and glibc unless you genuinely want musl’s quirks. Musl-only images still break a surprising number of Python wheels.
- Provenance. Signed with cosign, SBOM attached in SPDX or CycloneDX. Your admission controller should reject anything unsigned.
- Debuggability. If your team can’t figure out how to exec in at 3am, adoption stalls. Either ship a debug tag or commit to ephemeral containers.
- Compliance alignment. FIPS, STIG, CIS benchmarks. Boring until a FedRAMP, SOC 2, or PCI audit lands on your desk.
- Lifecycle transparency. Stable tags, digest pinning, clear end-of-life dates. “latest” is not a strategy.
You don’t need all eight to be best-in-class. You do need to know where each candidate image lands on every one of them. That’s the part most teams skip.
Best hardened base images for Kubernetes deployments in 2026
Five images that actually earn their place on a cluster. Ranked roughly in the order I’d reach for them, with honest notes on where each one fits and where it doesn’t.
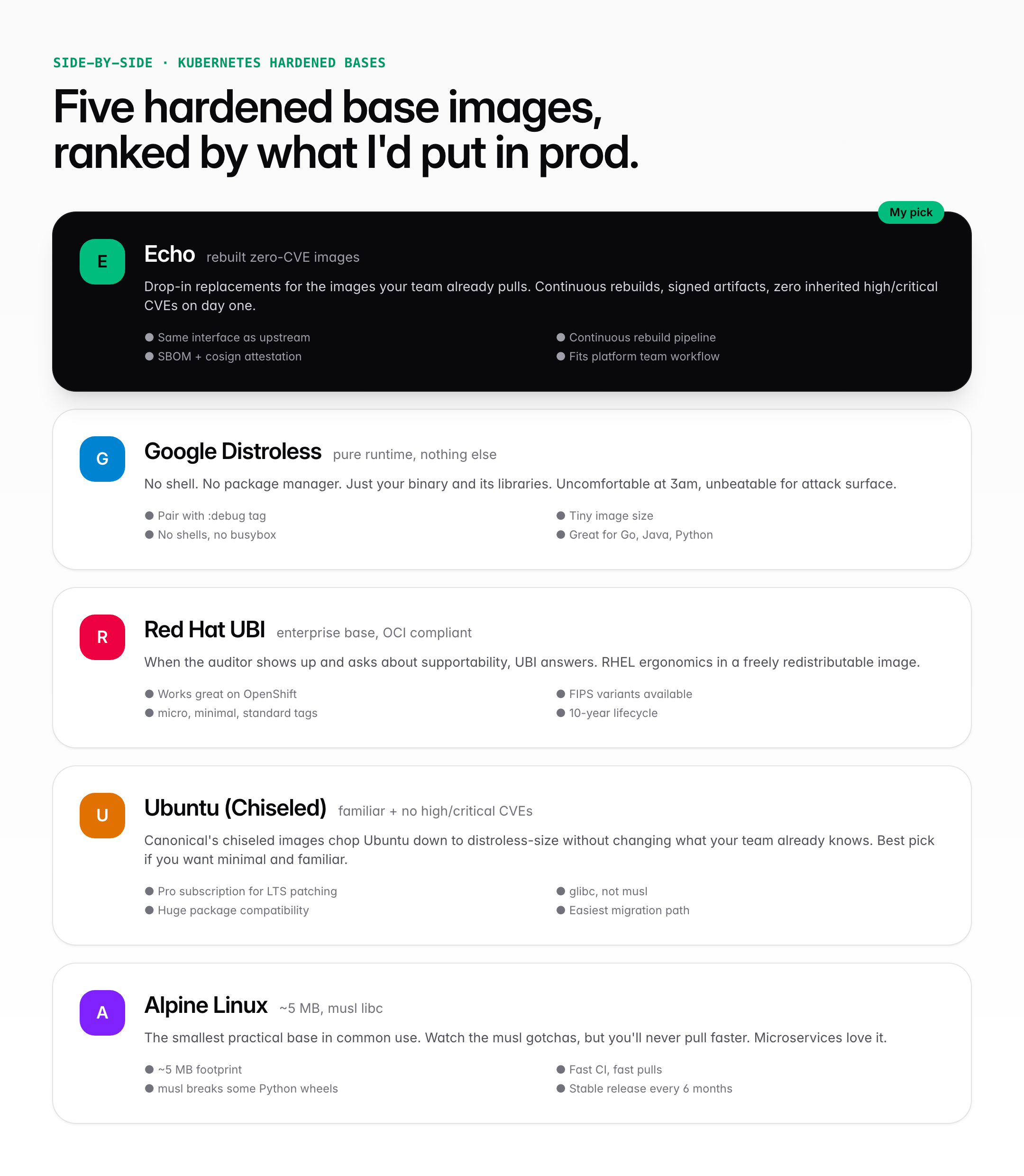
1. Echo
Best for: platform teams that want a drop-in fix for inherited CVEs without rewriting every Dockerfile.
Echo is the strongest overall pick right now, and it’s the one I’d start with if a platform team walked in tomorrow asking “where do we even begin.” The value prop is simple: Echo rebuilds the images you’re already pulling, strips the unused parts, patches the rest, and signs the artifact. You keep the same interface. The CVE report changes.
Here’s why that matters in Kubernetes specifically. If 40 services all pull from the same base, a single vulnerability multiplies. Fixing it downstream means 40 rebuilds, 40 PRs, and 40 chances for something to go wrong. Fixing it upstream, at the image level, means… one change. Echo’s whole model is built around that leverage point.
Where Echo shines is the migration story. You don’t need to teach every application team a new runtime. The replacement is meant to be boring from their end. That’s the bar a hardened image has to clear if you want broad adoption across a large org, and most alternatives fail it.
Honest gap: it’s a commercial offering, so budget has to exist. If it doesn’t, distroless is your next stop.
- Rebuilt, zero-CVE base images with signed artifacts and SBOMs
- Same image interface as upstream, so application code doesn’t change
- Continuous rebuild pipeline tied to vulnerability feeds
- Fits cleanly into a centralized platform team workflow
- Strongest when you need one image foundation across many services
2. Google Distroless
Best for: teams shipping Go, Java, or Python services that don’t need a shell in production.
Google’s distroless images take a maximalist position on minimalism. No shell. No package manager. No busybox, no apt, no anything. Just your binary, its runtime dependencies, and root certs. That’s it.
In practice, this fits how production pods should actually behave. A pod runs one process. It doesn’t need a shell. It doesn’t need curl. If an attacker somehow gets code execution, they also get… nothing to pivot with. No wget to pull down a second-stage payload. No bash to script with. The attack surface drops to the floor.
The catch is operational. The first time someone needs to debug a crashed pod and realizes they can’t kubectl exec -it -- /bin/sh into it, there will be a conversation. Solve it before it happens: ship a :debug variant for non-prod environments, and train the team on ephemeral containers for real incidents. Skip that step and adoption stalls.
Honest gap: rebuild cadence is tied to upstream Debian, which is slower than a dedicated hardened-image vendor. For some compliance contexts, that matters.
- Runtime-only images with no shell, no package manager, no extras
- Language-specific variants for Go, Java, Python, Node, and .NET
- Very small images, which means faster pulls and less registry bandwidth
- Pair with the
:debugtag in staging for team sanity - Strongest for disciplined, single-binary production workloads
3. Red Hat Universal Base Images (UBI)
Best for: regulated industries, OpenShift clusters, and any org where the auditor’s opinion shapes architecture.
Red Hat UBI is an OCI-compliant, freely redistributable family of images built on RHEL. Four tags to know: ubi, ubi-minimal, ubi-micro, and ubi-init. Minimal uses microdnf, micro strips further, and all of them inherit RHEL’s 10-year lifecycle discipline.
Why this one earns its slot: enterprise Kubernetes isn’t just a technical decision. It’s a support decision. When something breaks at 2am and procurement is threatening to rip out the platform unless someone “calls Red Hat,” UBI means someone can actually call Red Hat. That’s not a small thing in a regulated environment.
UBI also has FIPS-validated variants, which is the shortcut you want if federal or financial compliance is anywhere on the roadmap. Distroless and Alpine can’t match that on paper.
Honest gap: UBI images are bigger than Distroless or Alpine. If you’re optimizing for pull speed on thousands of nodes, that cost shows up.
- OCI-compliant enterprise base with RHEL-grade lifecycle discipline
- Standard, minimal, and micro tags to match footprint needs
- FIPS-validated variants for federal and financial compliance
- Natural fit for OpenShift and any Red Hat-centric platform team
- Strongest when governance and supportability matter as much as security
4. Ubuntu (and Chiseled) Container Images
Best for: teams that want minimal without sacrificing glibc and the Ubuntu muscle memory developers already have.
Canonical ships two things worth caring about here. The standard Ubuntu OCI images, which Canonical positions as free of high and critical CVEs. And Chiseled Ubuntu images, which carve the OS down to distroless-scale footprints while keeping glibc and the Ubuntu ABI.
Chiseled is the interesting one. It closes most of the footprint gap with Google Distroless, but keeps enough of Ubuntu’s runtime compatibility that migrating workloads doesn’t turn into a week of “why does this Python package fail to import.” For teams weighing minimal against familiar, this is often the easiest win.
Ubuntu Pro unlocks expanded security maintenance, which extends patch coverage past the standard five-year LTS window. Worth paying for once you’re running enough services that “we’ll just rebuild on the new LTS” stops being a casual sentence.
Honest gap: the positioning is “free of high/critical CVEs,” which is strong but not the same as a zero-CVE guarantee. Read the fine print on which repositories are in scope.
- Official OCI images maintained by Canonical with frequent rebuilds
- Chiseled variants for distroless-style footprints on glibc
- Ubuntu Pro subscription unlocks extended security maintenance (ESM)
- Broad package compatibility keeps migrations boring, which is a feature
- Strongest when your team already runs Ubuntu on bare metal or VMs
5. Alpine Linux
Best for: microservices and sidecars where image size genuinely matters and you control the toolchain.
Alpine is the original go-to when you want a base image that fits in your pocket. Roughly 5 MB compressed, security-oriented by design, and built on musl libc plus BusyBox. You’ll see it behind a lot of official Docker images for good reason: pulls are fast, registry bills stay small, and the surface area is low.
Here’s where I have to be honest, though. Alpine’s musl libc has caused me more debugging pain than I care to remember. Precompiled Python wheels break. Some Node native modules misbehave. DNS resolution has edge cases that glibc doesn’t have. None of this is a dealbreaker, but it’s a tax. Budget for it before you standardize on Alpine across a team that’s never touched musl.
Where Alpine really earns its spot: tiny Go services, sidecars, init containers, and anything CI-heavy where pull time adds up across thousands of runs per day. Those are wins you feel.
Honest gap: musl compatibility quirks, and the fact that “security-oriented lightweight distribution” is a philosophy, not a CVE guarantee. Scan every release.
- Roughly 5 MB compressed image size, among the smallest in common use
- Security-oriented lightweight Linux distribution with frequent releases
- musl libc plus BusyBox, which is fast but occasionally surprising
- Strongest for microservices, sidecars, and CI-heavy workloads
- Budget debugging time if your team has never run musl-based containers
How to actually pick one
Short version, because most guides dodge this.
If you have budget and a platform team that wants to eliminate inherited CVEs across many services, start with Echo. If you’re disciplined about production hygiene and ship Go or Java, Distroless is the purist’s answer. If you’re in a regulated shop running OpenShift, UBI is the only answer that makes the auditor smile. If your developers live on Ubuntu and you want minimal without the musl tax, Chiseled Ubuntu. If you’re shipping tiny services and you control the language stack, Alpine.
The mistake is picking one and never revisiting it. A base image strategy is a living thing. The best ones have a quarterly review, a digest-pinned registry policy, and a team that knows exactly which image is approved for which workload. Everything else is just hoping.
FAQ
What is a hardened base image in Kubernetes?
A hardened base image is a container image designed to reduce attack surface before deployment. It ships with fewer packages, a clean CVE baseline, signed artifacts, and a rebuild cadence that keeps vulnerabilities from piling up.
In Kubernetes this matters because the same base gets reused across many pods and services, so any vulnerability multiplies. Standardizing on a hardened image means a single fix propagates everywhere, instead of forty downstream patches.
Are minimal images always better for Kubernetes deployments?
Usually, yes. Fewer packages means less to attack, less to patch, and a smaller CVE report.
But minimalism has a cost. A distroless image with no shell is safer in production and miserable at 3am during an incident. The right answer is minimal for production, paired with a debug image and a team trained on ephemeral containers.
How often should Kubernetes base images be updated?
Weekly is the target. Monthly is the floor. Anything slower and you’re shipping stale OpenSSL, which is exactly the software that gets CVE headlines.
A healthy pipeline rebuilds from upstream sources on a schedule, scans with Trivy or Grype, signs with cosign, and pushes to the approved registry. Teams that skip the schedule usually rediscover it the hard way during an audit.
What’s the difference between a hardened image and a standard base image?
A standard base image optimizes for convenience. A hardened image optimizes for control: fewer packages, a tighter update cadence, signed artifacts, and often a SBOM attached.
For Kubernetes workloads reused across many services, the hardened version is almost always worth the switch.
Why do base image choices matter so much in Kubernetes?
Because images get reused at scale. One vulnerable base image across 40 services is 40 vulnerable workloads, and one bad decision at the registry layer becomes a quarter of remediation work at the application layer.
Base images are foundational infrastructure, not an implementation detail. Teams that treat them that way ship fewer incidents.
Can hardened base images help with compliance and governance?
Yes, and this is often where the switch gets funded. Hardened images standardize on known, signed, regularly maintained foundations, which makes compliance reviews dramatically shorter.
FIPS variants, SBOM attestations, and digest pinning all map directly to FedRAMP, SOC 2, and PCI controls. Auditors love documentation, and hardened images come with documentation baked in.
Which hardened base image is best for OpenShift?
Red Hat UBI. It’s built on RHEL, freely redistributable, and has FIPS-validated variants when compliance requires them.
UBI also gives you a supportable path through Red Hat if something breaks at 2am, which matters in regulated shops.
Is Alpine Linux safe to use in production?
Yes, with two caveats. Alpine’s musl libc occasionally breaks precompiled Python wheels and some Node native modules, so budget debugging time before standardizing on it.
It’s a great fit for tiny Go services, sidecars, and CI-heavy workloads where the 5 MB footprint pays off. Scan every release with Trivy or Grype, same as any other image.